Bad Rabbit ransomware! it multiply like rabbits
A new ransomware campaign has hit a number of high profile targets in Russia and Eastern Europe.
Dubbed Bad Rabbit, the ransomware first started infecting systems on Tuesday 24 October, and the way in which organizations appear to have been hit simultaneously immediately drew comparisons to this year's WannaCry and Petya epidemics.
The new strain of ransomware, dubbed Bad Rabbit, was first spotted on October 24. To date, the systems attacked have mostly been confined to Russia and Ukraine. The ransomware is the third major spread of malware this year: it follows the wider-reaching WannaCry and NotPetya strains of malicious code.
So what is Bad Rabbit?
The Bad Rabbit ransomware spreads through drive-by attacks" where insecure websites are compromised. "While the target is visiting a legitimate website, a malware dropper is being downloaded from the threat actor's infrastructure.
In this instance, the malware is disguised as an Adobe Flash installer. When the innocent-looking file is opened it starts locking the infected computer. The Flash download has been installed in websites using JavaScript injected into the HTML or Java files of the affected websites. The malware isn't installed automatically, which means it has to be clicked on to work.
If a person does click on the malicious installer - and given the number of Flash updates issued this is highly probable - their computer locks. The ransom note and payment page demands around $280 in Bitcoin and gives a 40-hour deadline for payments to be made. The DiskCryptor software is Bing used to encrypt hard-drives.
Who was affected?
Organizations across Russian and Ukraine -- as well as a small number in Germany, and Turkey -- have fallen victim to the ransomware. Researchers at Avast say they've also detected the malware in Poland and South Korea.
Other organizations in the region including Odessa International Airport and the Kiev Metro also made statements about falling victim to a cyber-attack, while CERT-UA, the Computer Emergency Response Team of Ukraine, also posted that the "possible start of a new wave of cyber attacks to Ukraine's information resources" had occurred, as reports of Bad Rabbit infections started to come in.
At the time of writing, it's thought there are almost 200 infected targets and indicating that this isn't an attack like WannaCry or Petya was -- but it's still causing problems for infected organizations.
It's definitely ransomware:
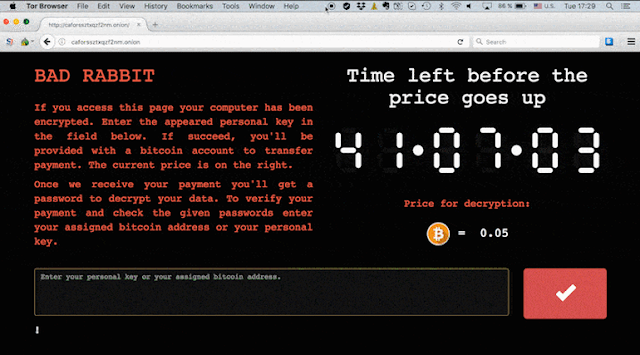
Those unfortunate enough to fall victim to the attack quickly realized what had happened because the ransomware isn't subtle -- it presents victims with a ransom note telling them their files are "no longer accessible" and "no one will be able to recover them without our decryption service".
Victims are directed to a Tor payment page and are presented with a countdown timer. Pay within the first 40 hours or so, they're told, and the payment for decrypting files is 0.05 bitcoin -- around $285. Those who don't pay the ransom before the timer reaches zero are told the fee will go up and they'll have to pay more.
The encryption uses DiskCryptor, which is open source legitimate and software used for full drive encryption. Keys are generated using CryptGenRandom and then protected by a hardcoded RSA 2048 public key.
It's based on Petya/Not Petya:
If the ransom note looks familiar, that's because it's almost identical to the one victims of June's Petya outbreak saw. The similarities aren't just cosmetic either -- Bad Rabbit shares behind-the-scenes elements with Petya too.
Analysis by researchers at Crowdstrike has found that Bad Rabbit and NotPetya's DLL (dynamic link library) share 67 percent of the same code, indicating the two ransomware variants are closely related, potentially even the work of the same threat actor.
It spreads via a fake Flash update on compromised websites:
The main way Bad Rabbit spreads is drive-by downloads on hacked websites. No exploits are used, rather visitors to compromised websites some of which have been compromised since June are told that they need to install a Flash update. Of course, this is no Flash update, but a dropper for the malicious install.
Infected websites -- mostly based in Russia, Bulgaria, and Turkey are compromised by having JavaScript injected in their HTML body or in one of their .js files.
It can spread laterally across networks:
Much like Petya, Bad Rabbit comes with a potent trick up its sleeve in that it contains an SMB component which allows it to move laterally across an infected network and propagate without user interaction, say researchers at Cisco Talos.
What aids Bad Rabbit's ability to spread is a list of simple username and password combinations which it can exploit to brute-force its way across networks. The weak passwords list consists of a number of the usual suspects for weak passwords such as simple number combinations and 'password'.
It doesn't use EternalBlue
When Bad Rabbit first appeared, some suggested that like WannaCry, it exploited the EternalBlue exploit to spread. However, this now doesn't appear to be the case.
"We currently have no evidence that the EternalBlue exploit is being utilized to spread the infection," Martin Lee, Technical Lead for Security Research at Talos told ZDNet.
It may not be indiscriminate
At the same point following the WannaCry outbreak, hundreds of thousands of systems around the world had fallen victim to ransomware. However, Bad Rabbit doesn't appear to indiscriminately infecting targets, rather researchers have suggested that it only infects selected targets.
"Our observations suggest that this been a targeted attack against corporate networks," said Kaspersky Lab researchers.
Meanwhile, researchers at ESET say instructions in the script injected into infected websites "can determine if the visitor is of interest and then add content to the page" if the target is deemed suitable for infection.
However, at this stage, there's no obvious reason why media organizations and infrastructure in Russia and Ukraine has been specifically targeted in this attack.
It isn't clear who is behind it:
At this time, it's still unknown who is distributing the ransomware or why, but the similarity to Petya has led some researchers to suggest that Bad Rabbit is by the same attack group -- although that doesn't help identify the attacker or the motive either, because the perpetrator of June's epidemic has never been identified.
What marks this attack out is how it has primarily infected Russia - Eastern Europe cybercriminal organizations tend to avoid attacking the 'motherland', indicating this unlikely to be a Russian group.
It contains Game of Thrones references:
Whoever it behind Bad Rabbit, they appear to be a fan of Game of Thrones: the code contains references to Viserion, Drogon, and Rhaegal, the dragons which feature in television series and the novels it is based on. The authors of the code are therefore not doing much to change the stereotypical image of hackers being geeks and nerds.
You can protect yourself against becoming infected by it
At this stage, it's unknown if it's possible to decrypt files locked by Bad Rabbit without giving in and paying the ransom - although researchers say that those who fall victim shouldn't pay the fee, as it will only encourage the growth of ransomware.
A number of security vendors say their products protect against Bad Rabbit. But for those who want to be sure they don't potentially fall victim to the attack, Kaspersky Lab says users can block the execution of file 'c: \ windows \ infpub.dat, C: \ Windows \ cscc.dat.' in order to prevent infection.





Comments
Post a Comment